Highlights:
- Before blocking, muting, and reporting, it’s important to document cyberbullying incidents for evidence.
- Screenshots are one of the simplest and most effective means of documentation.
- There are various places to report cyberbullying incidents, depending on what the incident is and what the victim wants to see happen.
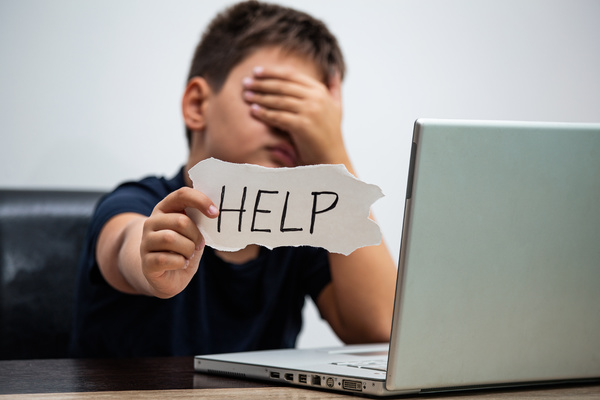
If there’s one thing that nearly all kids or teens experience at some point, it’s bullying. Kids that aren’t bullied are often engaging in bullying behavior themselves, and nearly all kids witness it. And now, with so much of a child’s social and school life taking place online, cyberbullying is even more prevalent than it ever was before. It’s more important than ever for young people to know how to deal with cyberbullying – how to block and mute the bullies and how to report them as necessary. And that means that parents need to know as well.
What to Do First
“Block, mute, and report” is the advice given to a lot of kids and teens when dealing with bullies online. But what should they do first, and how?
It’s not on the list, but what your child really should be doing when they experience cyberbullying is document what happened. When they report the incident, they will most likely be asked for evidence. Once they’ve blocked or muted the users who were bullying them, they may no longer have access to the offending messages or posts, depending on what platform they’re on. Or the bully may remove them (or the platform might). So documentation is an important first step.
After documenting what’s happening, your child should protect themselves by blocking or muting the bully so that they no longer have to see or receive bullying posts or messages. Then it’s time to decide who to report the incident to and make the report.
How to Document Cyberbullying
When a bully is reported for attacking a victim, they don’t just accept it and admit to it. Quite the opposite, in fact – when a victim reports a bully, a common response is for the bully to use a tactic known as DARVO (Deny, Attack, Reverse Victim and Offender). Essentially, they try to blame the victim instead of taking responsibility for their actions.
Having documentation not only proves who said or did what and when to any authorities that the cyberbullying is reported to, but it also helps the victim keep the sequence of events straight in their mind. When your is child upset, it can be easier than you may think to cause them to start questioning themselves when a bully insists that they’re the aggressor.
Screenshots are a good way to document cyberbullying. They can be taken on basically any device, and they can be downloaded to the device and saved somewhere under the control of the user, not on the app or websites.
In a few cases, screenshots are prevented or made more difficult by notifying the user. (Snapchat is a good example.) But kids should still do the best they can to document incidents on these platforms, such as writing down or audio recording the time, date, and all the details as soon as they can following the incident.
Block or Mute
Blocking and muting are both steps that your child can take to protect themselves from having to see or interact with bullying content. And they should certainly take those steps; it won’t do them any good to continue to interact with a bully. Whether they block or mute and what those actions mean depends on the situation and the website or app they’re using.
Blocking usually applies to the account. So when your child blocks someone, they block the entire account, meaning that the blocker can no longer see that person or their activity or messages, and the blocked person can no longer see or message the blocker.
Muting is a little more targeted. It hides content from the user who does the muting but does not necessarily hide the entire account. You may be able to block messages, hashtags or keywords, or specific posts without losing access to the account.
In many bullying situations, blocking is the way to go, especially if the cyberbully is a real-life stranger. It cleanly cuts them out of your child’s social media world. But in some cases, muting might be the way to go instead.
How to Report

After documenting and blocking or muting, what’s left? Reporting. But who do you report a cyberbully to?
One thing your child should do first is report the incident to you or to another trusted adult in their lives. They will then have an adult who’s aware of the situation in case it escalates and can help them decide what to do next.
The next step is to decide who else to report the incident to. Some options include:
- The platform. If the cyberbullying happens on a social media site, it’s probably against the terms of service for the site or app.
- The service provider. When a bully is using their internet or cell phone service to harass, they may be violating the terms of their agreement with the service provider, so it can be reported to them as well.
- The school. Cyberbullying incidents between two children who attend the same school may either have already had a conflict in person (or will have one) because of cyberbullying. Letting the school know what happened gives them the ability to ensure your child’s safety and enforce any school rules that apply to the situation.
- Law enforcement. If the cyberbullying situation reaches a certain level, law enforcement will need to be brought in, especially if there are threats of violence, serious violations of privacy, hate crimes, or child pornography involved.
Parental monitoring software like WebWatcher can help you keep an eye on your child’s online activity and on top of any cyberbullying situations. To find out more about how WebWatcher can help, get our free trial.





